
Replace 4/19/26: Added extra info from Vercel that was disclosed after publishing.
Cloud improvement platform Vercel has disclosed a safety incident after menace actors claimed to have breached its programs and are trying to promote stolen information.
Vercel is a cloud platform that gives internet hosting and deployment infrastructure for builders, with a robust concentrate on JavaScript frameworks.
The corporate is identified for creating Subsequent.js, a extensively used React framework, and for providing providers corresponding to serverless capabilities, edge computing, and CI/CD pipelines that allow builders to construct, preview, and deploy purposes.
In a safety bulletin printed in the present day, the corporate stated a restricted subset of consumers was affected by a safety breach.
“We have recognized a safety incident that concerned unauthorized entry to sure inner Vercel programs,” warns Vercel.
“We’re actively investigating, and now we have engaged incident response consultants to assist examine and remediate. We’ve got notified regulation enforcement and can replace this web page because the investigation progresses.”
The corporate says its providers haven’t been impacted and that it’s working with impacted clients.
Vercel says it’s taking steps to guard its clients, advising them to evaluate surroundings variables, use its delicate surroundings variable characteristic, and to rotate secrets and techniques if wanted.
After publishing this story, Vercel up to date its advisory to state that the breach stemmed from the compromise of a third-party AI software’s Google Workspace OAuth software.
Vercel is advising Google Workspace directors and Google account homeowners to test for the next software:
OAuth App: 110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com
Vercel CEO Guillermo Rauch later shared extra particulars on X, stating that the preliminary entry occurred after a Vercel worker’s Google Workspace account was compromised by way of a breach on the AI platform Context.ai.
In response to Rauch, the attacker then escalated entry from the compromised account into Vercel environments, the place they have been capable of entry surroundings variables that weren’t marked as delicate and subsequently not encrypted at relaxation.
Whereas meant to include non-sensitive info, the attacker gained additional entry after enumerating these variables.
“Vercel shops all buyer surroundings variables absolutely encrypted at relaxation. We’ve got quite a few defense-in-depth mechanisms to guard core programs and buyer information,” Rauch stated.
“We do have a functionality, nevertheless, to designate surroundings variables as ‘non-sensitive.’ Sadly, the attacker received additional entry by means of their enumeration.”
The corporate’s investigation has confirmed that Subsequent.js, Turbopack, and its different open-source initiatives stay secure.
Vercel has additionally rolled out updates to its dashboard, together with an outline web page of surroundings variables and an improved interface for managing delicate surroundings variables.
Clients are strongly suggested to evaluate surroundings variables for delicate info and allow the delicate variable characteristic to make sure they’re encrypted at relaxation.
If in case you have any info relating to this incident or different undisclosed assaults, you’ll be able to contact us confidentially by way of Sign at 646-961-3731 or at suggestions@bleepingcomputer.com.
Hacker claims to be promoting stolen Vercel information
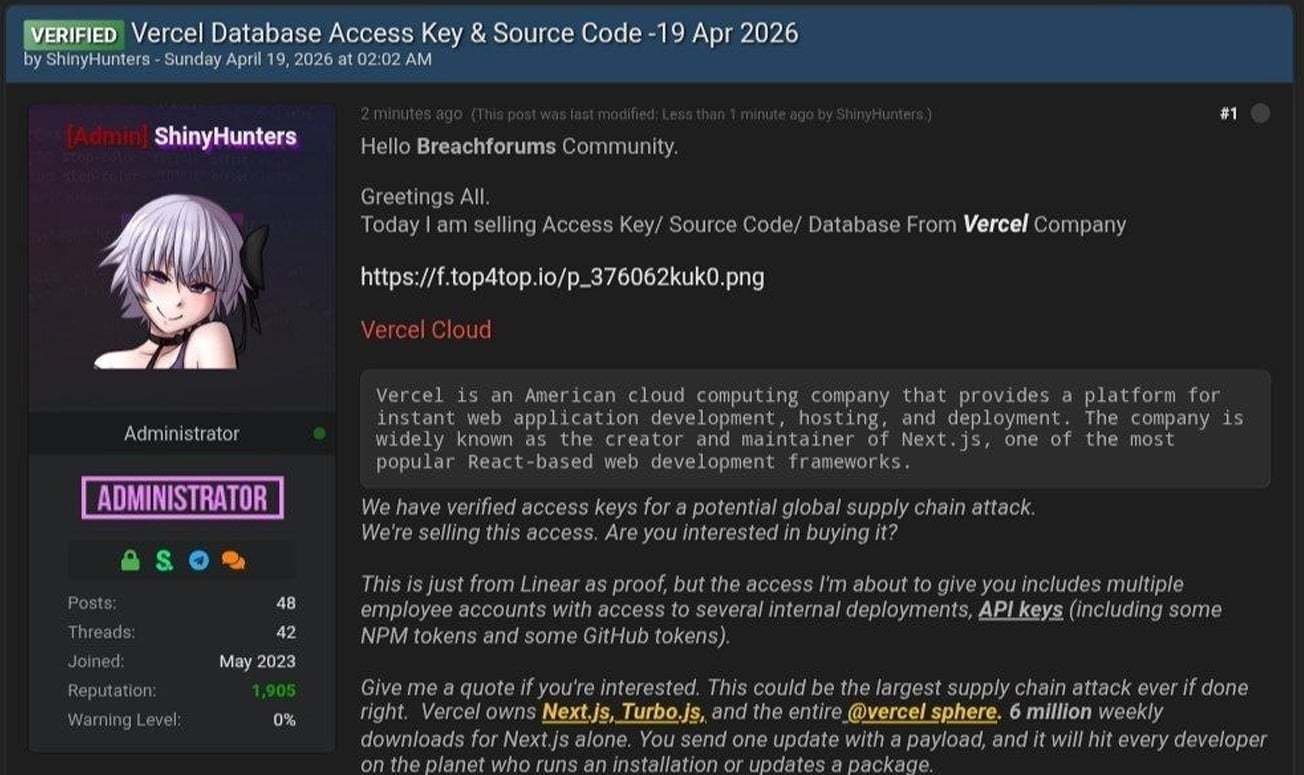
The disclosure comes after a menace actor claiming to be “ShinyHunters” posted on a hacking discussion board that they’d breached Vercel and have been promoting entry to firm information.
It ought to be famous that whereas the hacker claims to be a part of the ShinyHunters group, menace actors linked to latest assaults attributed to the ShinyHunters extortion gang have denied to BleepingComputer that they’re concerned on this incident.
Within the discussion board submit, the hacker claimed to be promoting entry keys, supply code, and database information allegedly stolen from Vercel, together with entry to inner deployments and API keys.
“That is simply from Linear as proof, however the entry I am about to offer you contains a number of worker accounts with entry to a number of inner deployments, API keys (together with some NPM tokens and a few GitHub tokens),” reads the discussion board submit.
The attacker additionally shared a textual content file containing Vercel worker info, which consists of 580 information information containing names, Vercel electronic mail addresses, account standing, and exercise timestamps. In addition they shared a screenshot of what seems to be an inner Vercel Enterprise dashboard.
BleepingComputer has not been capable of independently affirm if the info or screenshot is genuine.
In messages shared on Telegram, the menace actor additionally claimed they have been involved with Vercel relating to the incident and that they mentioned an alleged ransom demand of $2 million.
BleepingComputer contacted Vercel with extra questions in regards to the breach, together with whether or not any delicate information or credentials have been uncovered and if they’re negotiating with the attackers, and can replace this story if we obtain a response.
Replace 4/19/26 6:14 PM ET: Up to date article so as to add additional info disclosed by Vercel.
Replace 4/19/26 7:21 PM ET: Up to date article with extra info from Vercel’s CEO.
AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Autonomous Validation Summit (Might 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.



