.jpg)
A brand new variant of the TrickMo Android banking malware, delivered in campaigns concentrating on customers throughout Europe, introduces new instructions and makes use of The Open Community (TON) for stealthy command-and-control communications.
The TrickMo banker was first noticed in September 2019 and has remained in energetic improvement, consistently receiving updates since then.
In October 2024, Zimperium analyzed 40 variants of the malware delivered through 16 droppers, speaking with 22 distinct command-and-control (C2) infrastructures, and concentrating on delicate information belonging to customers worldwide.
The newest variant was found by ThreatFabric, which tracks it as ‘Trickmo.C’. The researchers have been observing this model since January.
In a report at present, ThreatFabric says that the malware is disguised as TikTok or streaming apps and targets banking and cryptocurrency wallets of customers in France, Italy, and Austria.
The important thing new function within the present variant is the TON-based communication with the operator, which makes use of .ADNL addresses routed by means of an embedded native TON proxy operating on the contaminated system.
TON is a decentralized peer-to-peer community initially developed across the Telegram ecosystem that enables gadgets to speak with the online through an encrypted overlay community quite than publicly uncovered web servers.
TON makes use of a 256-bit identifier as a substitute of a standard area, which hides the IP tackle and communication port, thus making the true server infrastructure harder to determine, block, or take down.
“Conventional area takedowns are largely ineffective as a result of the operator’s endpoints don’t depend on the general public DNS hierarchy and as a substitute exist as TON .adnl identities resolved contained in the overlay community itself,” explains ThreatFabric.
“Site visitors-pattern detection on the community edge sees solely TON visitors, which is encrypted and indistinguishable from every other TON-enabled software’s outbound movement.”
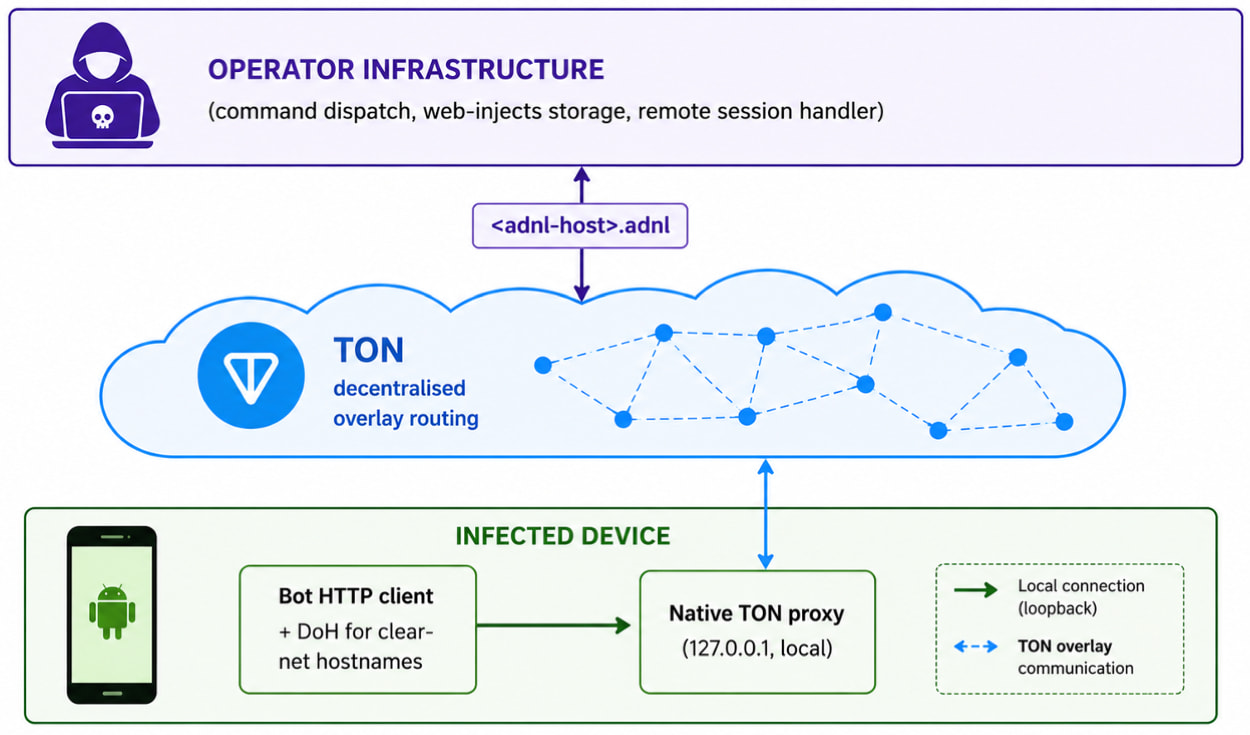
Supply: ThreatFabric
TrickMo’s capabilities
TrickMo is a modular malware with a two-stage design: a number APK that serves because the loader and persistence layer, and a runtime-downloaded APK module that implements the offensive performance.
The malware targets banking credentials through phishing overlays, performs keylogging, display screen recording, and dwell display screen streaming, SMS interception, OTP notification suppression, clipboard modification, notification filtering, and screenshot capturing.
ThreatFabric experiences that the brand new variant provides the next instructions and capabilities:
- curl
- dnsLookup
- ping
- telnet
- traceroute
- SSH tunneling
- distant port forwarding
- native port forwarding
- authenticated SOCKS5 proxy assist
The researchers have additionally noticed the Pine runtime hooking framework, beforehand used to intercept networking and Firebase operations, however it’s at present inactive as there are not any hooks put in.
TrickMo additionally declares intensive NFC permissions and experiences NFC capabilities in telemetry, however the researchers didn’t discover any energetic NFC performance.
Android customers are suggested to solely obtain software program from Google Play, restrict the variety of put in apps on their telephones, use apps solely from respected publishers, and be certain that Play Shield is energetic always.
AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Autonomous Validation Summit (Could 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.

.jpg?w=696&resize=696,0&ssl=1)
