
A brand new Android malware has been found hidden inside trojanized variations of the Alpine Quest mapping app, which is reportedly utilized by Russian troopers as a part of battle zone operational planning.
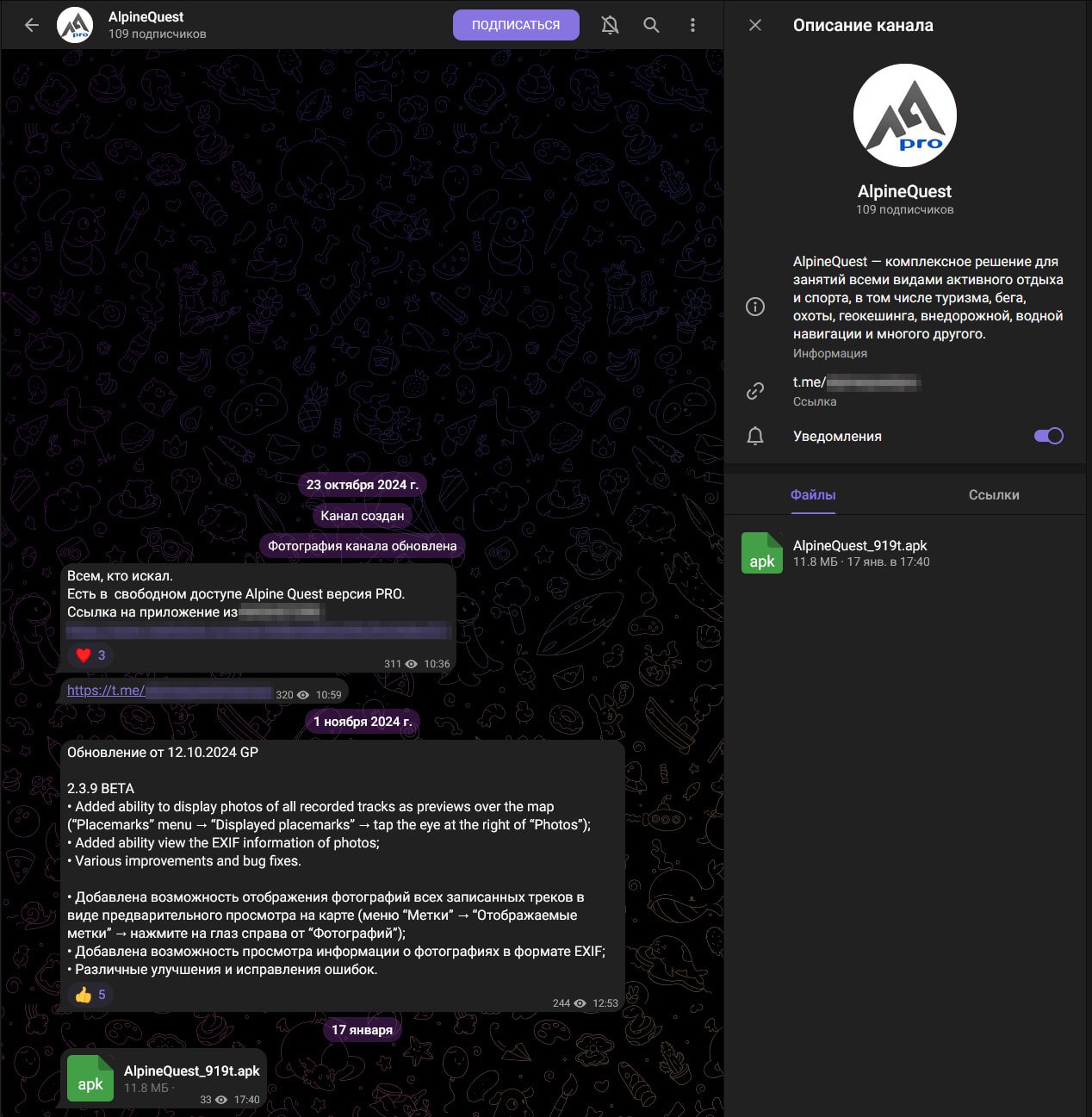
Attackers promote the trojanized app as a free, cracked model of the premium Alpine Quest Professional, utilizing Telegram channels and Russian app catalogs for distribution.
AlpineQuest is a professional GPS and topographic mapping app for Android utilized by adventurers, athletes, search-and-rescue groups, and army personnel, valued for its offline capabilities and precision.
The app has two variations: a free Lite model with restricted options and a paid Professional model that is freed from monitoring libraries, analytics, and ads.
The spy ware, which was found by researchers at Russian cellular antivirus firm Physician Net, hides inside a totally working Alpine Quest app, lowering suspicion and creating beneficial information theft alternatives.
As soon as launched, it makes an attempt to steal communication information and delicate paperwork from the gadget, probably revealing particulars about military operations. Particularly, the spy ware performs the next actions:
- Sends the consumer’s telephone quantity, contacts, geolocation, file information, and app model to attackers.
- Displays location modifications in real-time and sends updates to a Telegram bot.
- Downloads further modules to steal confidential information, particularly these despatched through Telegram and WhatsApp.
- Seeks the ‘locLog’ file from Alpine Quest, which accommodates location historical past logs.
Physician Net tracks the beforehand undocumented spy ware as ‘Android.Spy. 1292.origin’ however didn’t make any attributions about its origin in its report. Indicators of compromise are out there right here.
Supply: Physician Net
Turning the tables
The tactic of concentrating on troopers was beforehand related to Russian hacking operations, usually linked to state-sponsored menace teams amassing intelligence for the Russian military.
In December 2022, hackers utilizing a compromised Ukrainian Ministry of Protection electronic mail account tried subsequent infections by utilizing DELTA, a Ukrainian intelligence assortment and administration system as bait.
In October 2024, the Russian menace group ‘UNC5812’ focused Ukrainian conscripts with Home windows and Android malware through a pretend company named ‘Civil Protection.’
Extra just lately, in February 2025, Google researchers revealed that Russian menace actors of the APT44 group used malicious QR codes to trick targets into syncing their Sign accounts with unauthorized gadgets.
The invention of the trojanized AlpineQuest app reveals that these sneaky assaults are orchestrated from each ends of the battle, as intelligence assortment stays essential in gaining battlefield benefit.

