A brand new variant of the Mirai malware botnet is exploiting a command injection vulnerability in TBK DVR-4104 and DVR-4216 digital video recording units to hijack them.
The flaw, tracked below CVE-2024-3721, is a command injection vulnerability disclosed by safety researcher “netsecfish” in April 2024.
The proof-of-concept (PoC) the researcher revealed on the time got here within the type of a specifically crafted POST request to a weak endpoint, attaining shell command execution by the manipulation of sure parameters (mdb and mdc).
Kaspersky now stories having caught energetic exploitation of CVE-2024-3721 in its Linux honeypots from a brand new Mirai botnet variant utilizing netsecfish’s PoC.
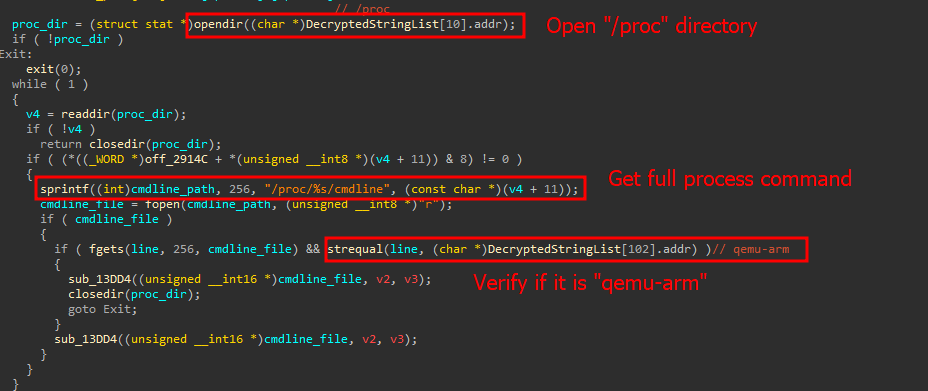
The attackers leverage the exploit to drop an ARM32 malware binary, which establishes communication with the command and management (C2) server to enlist the gadget to the botnet swarm. From there, the gadget is probably going used to conduct distributed denial of service (DDoS) assaults, proxy malicious visitors, and different habits.
Supply: Kaspersky
Assault impression and fixes
Though netsecfish reported final yr that there have been roughly 114,000 internet-exposed DVRs weak to CVE-2024-3721, Kaspersky’s scans present roughly 50,000 uncovered units, which continues to be important.
Most infections the Russian cybersecurity agency sees as being related to the newest Mirai variant impression China, India, Egypt, Ukraine, Russia, Turkey, and Brazil. Nonetheless, that is primarily based on Kaspersky’s telemetry, and as its client safety merchandise are banned in lots of nations, this will not precisely replicate the botnet’s concentrating on focus.
At present, it’s unclear if the seller, TBK Imaginative and prescient, has launched safety updates to handle the CVE-2024-3721 flaw or if it stays unpatched. BleepingComputer contacted TBK to ask about this, however we’re nonetheless ready for his or her response.
It is price noting that DVR-4104 and DVR-4216 have been extensively re-branded below the Novo, CeNova, QSee, Pulnix, XVR 5 in 1, Securus, Evening OWL, DVR Login, HVR Login, and MDVR manufacturers, so the provision of patches for impacted units is a posh matter.
The researcher who disclosed the TBK Imaginative and prescient flaw found different flaws that fueled exploitation in opposition to end-of-life units final yr.
Particularly, netsecfish has disclosed a backdoor account difficulty and a command injection vulnerability impacting tens of hundreds of EoL D-Hyperlink units in 2024.
Lively exploitation was detected in each instances only some days after the PoC’s disclosure. This reveals how rapidly malware authors incorporate public exploits into their arsenal.


