
The Federal Police in Germany (BKA) has recognized two Russian nationals because the leaders of GandCrab and REvil ransomware operations between 2019 and 2021.
Based on BKA’s disclosure, 31-year-old Daniil Maksimovich Shchukin and 43-year-old Anatoly Sergeevitsch Kravchuk acted because the heads of the 2 ransomware teams “from not less than the start of 2019 till not less than July 2021.”
Shchukin hid behind the monikers UNKN/UNKNOWN for years, posting on cybercrime boards and talking as a consultant of the ransomware operation.
The German authorities say that Shchukin and Kravchuk participated in not less than 130 extortion instances concentrating on corporations within the nation particularly.
Following these assaults, not less than 25 victims paid Shchukin and his co-conspirators $2.2 million in ransom, whereas the whole monetary harm brought on by them is estimated in extra of $40 million.
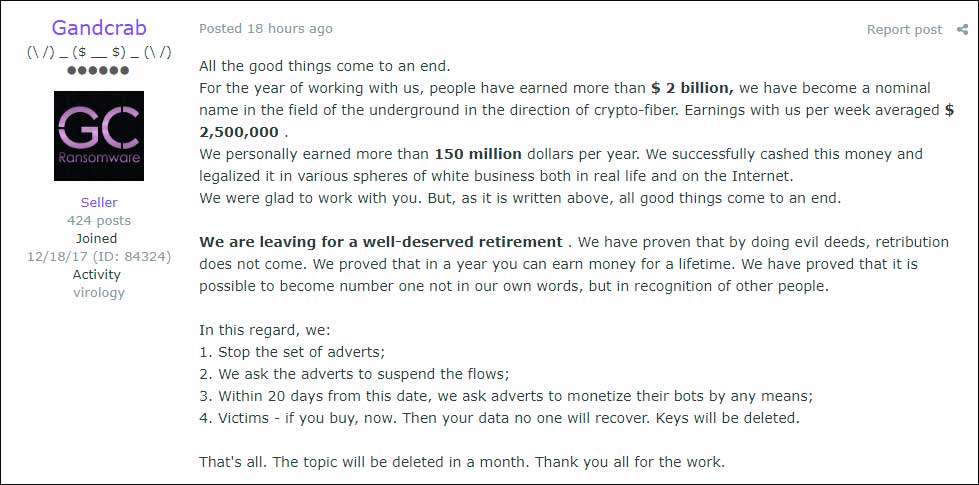
GandCrab began in early 2018, and its chief on the time determined to retire in June 2019, after claiming to have earned $2 billion from ransom funds. The chief, nevertheless, cashed out with $150 million, which they claimed to have invested in authorized companies.
supply: BleepingComputer
Quickly after, a brand new operation known as REvil emerged, following the affiliate mannequin established by GandCrab by promoting and constructing partnerships with cybercriminals.
REvil, also called Sodinokibi, was fashioned from earlier GandCrab associates and operators who had already discovered the profitable ways and began to use them to their operations.
REvil later added public leak websites and ran information auctions to strain victims. Notable victims embody a number of Texas native governments, laptop large Acer, and the Kaseya supply-chain assault that impacted round 1,500 downstream victims.
Following the large Kaseya hack, REvil took a two-month break, throughout which legislation enforcement breached their servers and began to watch operations.
A number of infrastructure disruptions have been recorded on the time, and in mid-January 2022, Russia arrested greater than a dozen REvil gang members, who have been launched in 2025 after time served on carding prices.
It’s unclear if both Shchukin or Kravchuk joined different ransomware operations following REvil’s demise in 2021.
BKA believes that Shchukin and Kravchuk at the moment are in Russia and asks the general public to share any info that would result in their whereabouts. Related entries have been additionally created on the EU’s Most Wished portal.
The police shared a number of photos, together with tattoo images, to assist observe down the 2 menace actors and produce them to justice.
Automated pentesting proves the trail exists. BAS proves whether or not your controls cease it. Most groups run one with out the opposite.
This whitepaper maps six validation surfaces, exhibits the place protection ends, and offers practitioners with three diagnostic questions for any software analysis.



