
Google API keys for companies like Maps embedded in accessible client-side code might be used to authenticate to the Gemini AI assistant and entry personal knowledge.
Researchers discovered almost 3,000 such keys whereas scanning web pages from organizations in varied sectors, and even from Google.
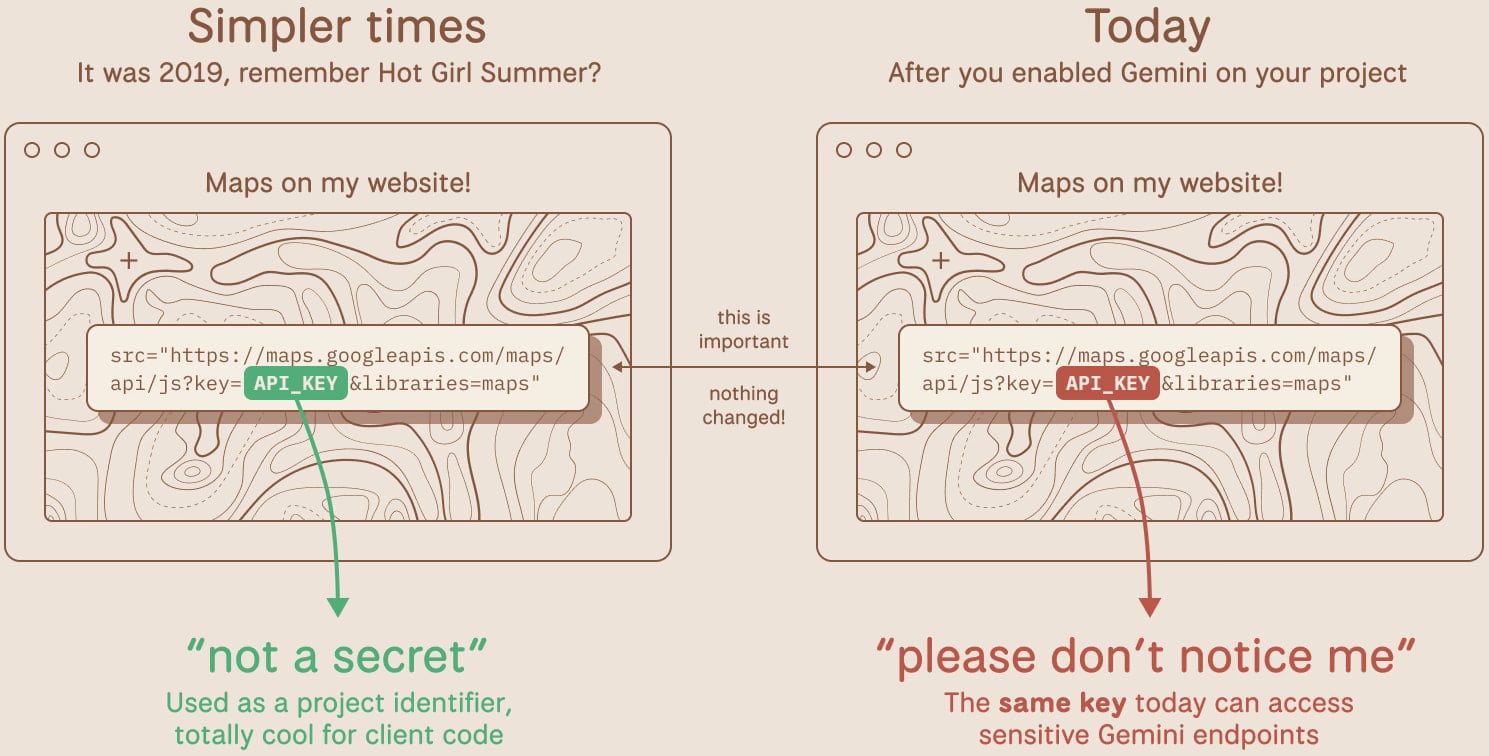
The issue occurred when Google launched its Gemini assistant, and builders began enabling the LLM API in initiatives. Earlier than this, Google Cloud API keys weren’t thought of delicate knowledge and might be uncovered on-line with out danger.
Builders can use API keys to increase performance in a venture, similar to loading Maps on an internet site to share a location, for YouTube embeds, utilization monitoring, or Firebase companies.
When Gemini was launched, Google Cloud API keys additionally acted as authentication credentials for Google’s AI assistant.
Researchers at TruffleSecurity found the difficulty and warned that attackers might copy the API key from an internet site’s web page supply and entry personal knowledge obtainable by the Gemini API service.
Since utilizing the Gemini API is just not free, an attacker might leverage the entry and make API calls for his or her profit.
“Relying on the mannequin and context window, a menace actor maxing out API calls might generate hundreds of {dollars} in prices per day on a single sufferer account,” Truffle Safety says.
The researchers warn that these API keys have been sitting uncovered in public JavaScript code for years, and now they’ve instantly gained extra harmful privileges with out anybody noticing.
TruffleSecurity scanned the November 2025 Widespread Crawl dataset, a consultant snapshot of a big swath of the preferred websites, and located greater than 2,800 reside Google API keys publicly uncovered of their code.
In accordance with the researchers, a number of the keys have been utilized by main monetary establishments, safety corporations, and recruiting corporations. They reported the issue to Google, offering samples from its infrastructure.
In a single case, an API key appearing simply as an identifier was deployed since at the very least February 2023 and was embedded within the web page supply of a Google product’s public-facing web site.
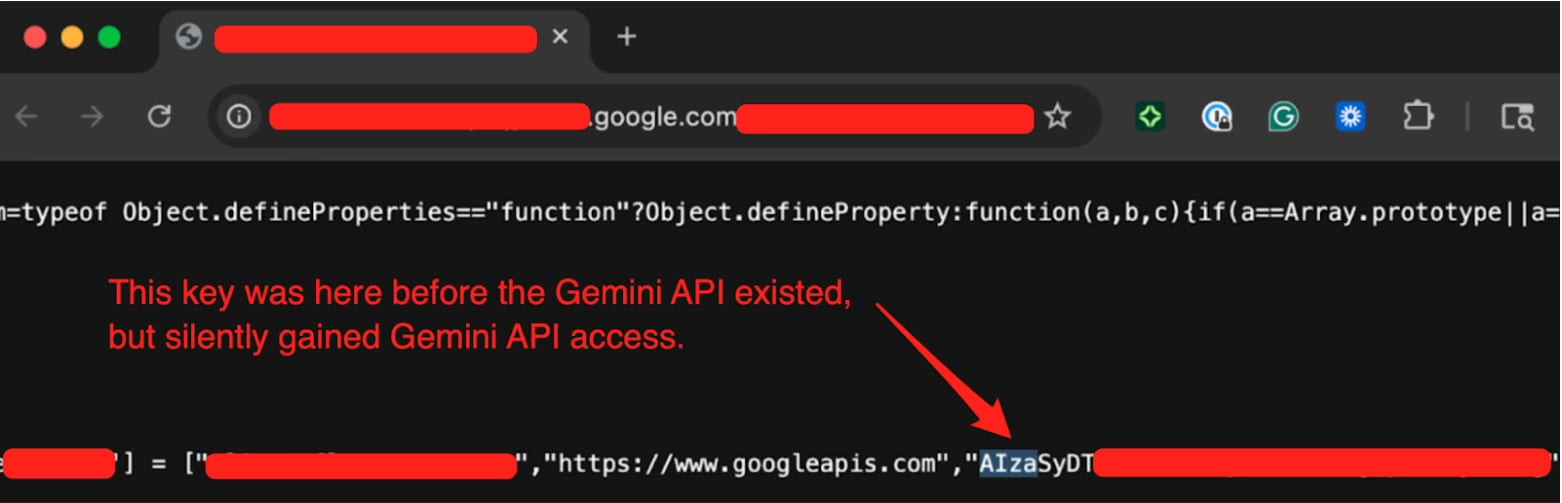
Supply: TruffleSecurity
Truffle Safety examined the important thing by calling the Gemini API’s /fashions endpoint and itemizing obtainable fashions.
The researchers knowledgeable Google of the issue final 12 months on November 21. After a protracted trade, Google categorised the flaw as “single-service privilege escalation” on January 13, 2026.
In a press release for BleepingComputer, Google says that it’s conscious of the report and has “labored with the researchers to handle the difficulty.”
“We now have already carried out proactive measures to detect and block leaked API keys that try and entry the Gemini API,” a Google spokesperson informed BleepingComputer.
Google said that new AI Studio keys will default to Gemini-only scope, leaked API keys can be blocked from accessing Gemini, and proactive notifications can be despatched when leaks are detected.
Builders ought to test whether or not Gemini (Generative Language API) is enabled on their initiatives and audit all API keys of their setting to find out if any are publicly uncovered, and rotate them instantly.
The researchers additionally recommend utilizing the TruffleHog open-source software to detect reside, uncovered keys in code and repositories.
Fashionable IT infrastructure strikes quicker than handbook workflows can deal with.
On this new Tines information, learn the way your staff can scale back hidden handbook delays, enhance reliability by automated response, and construct and scale clever workflows on high of instruments you already use.



